With know-how and a systematic approach
How can the cybersecurity compliance of products and components or entire machines be implemented in practice? There are no one-fits-all solutions. The level of risk exposure in each individual case is the crucial factor. Therefore, all distributors (manufacturers, resellers, importers) are required to carry out a cybersecurity risk assessment under the Cyber Resilience Act. The findings from this assessment must be documented and suitable measures implemented.
What many stakeholders may initially find unsettling and may seem alarming at first becomes achievable as soon as it has been practiced and implemented successfully.
Change of perspective for risk assessment
It is crucial to adopt a systematic approach. This starts with a change of perspective. Those responsible should look at their own product, machine or system from the perspective of a potential intruder and treat it in exactly the same way: get hold of plans and scrutinize the system for any inadequately secured doors and efficient routes inside. You don’t even have to be a security expert to do this. Engineers are used to solving tricky problems. It is just the approach to carrying out a risk assessment that is different. Instead of establishing functions, it is all about penetrating a system, manipulating it intentionally or accidentally, spying on it, sabotaging it or denying responsibility.
When it comes to intrusion from the outside, you first need to define what “outside” means. The gateway of choice for machines and systems is data communication. The CRA therefore states early on in Article 2 that it relates to products with data communication.
Experience shows that, when engineers focus on the cybersecurity of these products, they create economically efficient solutions that can be used in practice. Overshoots as a result of overfulfilling standards that at the same time are often inadequate are avoided. These can arise if specially commissioned experts implement expensive IT security measures to combat risks that are only theoretically conceivable.
To provide users with effective support, Beckhoff also offers, for its full range of automation components, guides on how to use them in a cybersecure way.
So, cybersecurity is not a fixed state, but an ongoing task
When it comes to the cybersecurity of components and products, the simple principle of “If you stop improving, you stop being good" applies. After all, what may have been cybersecure two years ago may now already be insecure, for example because the operating situation has changed or the technology has moved on – this applies to operators and manufacturers in equal measure. This is why cybersecurity needs to be reviewed on an ongoing basis and adapted accordingly if necessary – this also applies to components or machines and systems that have already been delivered.
This process requires suitable organizational measures. The Cyber Resilience Regulation 2024/2847/EU, more commonly known as the Cyber Resilience Act (CRA) [Link], sets out what these measures must achieve. The legislation stipulates that the following three aspects must be guaranteed throughout the supply chain and also for products that have already been delivered:
- For each product specimen, a support period must be clearly specified at the time of provision (for example, when the contract is concluded by means of a purchase or leasing agreement) with an end date in the form of a month and year.
- By no later than the specified date, the distributor of the product must ensure that any cybersecurity vulnerabilities in the product are actively monitored, assessed, exploitable vulnerabilities are addressed and remedies for them are provided free of charge, ideally in the form of updates, but otherwise also through the recall or withdrawal of the product.
- During the support period according to the CRA, the distributor must revise the risk assessment for the product at reasonable intervals and adjust it if necessary. This may result in cybersecurity updates for the product and improvements to the information provided to users.
According to the CRA, the support period should reflect the useful life of the product specimen, but may be shorter under certain conditions. It commences when the goods are placed on the market, even if they are initially still stored in a warehouse. The support period may only be less than five years if the product generally has a shorter service life. One example of a reason for shortening the support period is where a machine builder has installed in its product a supplied component with a core function for which a shorter support period applies. The service life of the machine itself may be significantly longer.
The support period as a minimum guarantee
The support period is a minimum guarantee period that can be exceeded. After the end of the support period, the distributor is free to offer the rectification of cybersecurity vulnerabilities and other services on a voluntary basis – this no longer has to be free of charge, but can be subject to conditions they set themselves.
This is only fair. The products made by machine builders in particular are often so durable that their expected useful life cannot be a benchmark for the length of the support period. If this were the case, machine builders would, for example, have to replace the operating system or parts of a machine’s hardware multiple times over the years free of charge in order to fix any vulnerabilities. Doing this voluntarily beyond the support period in return for appropriate compensation for costs is a far better approach that makes more economic sense.
Organizational tasks related to the support period
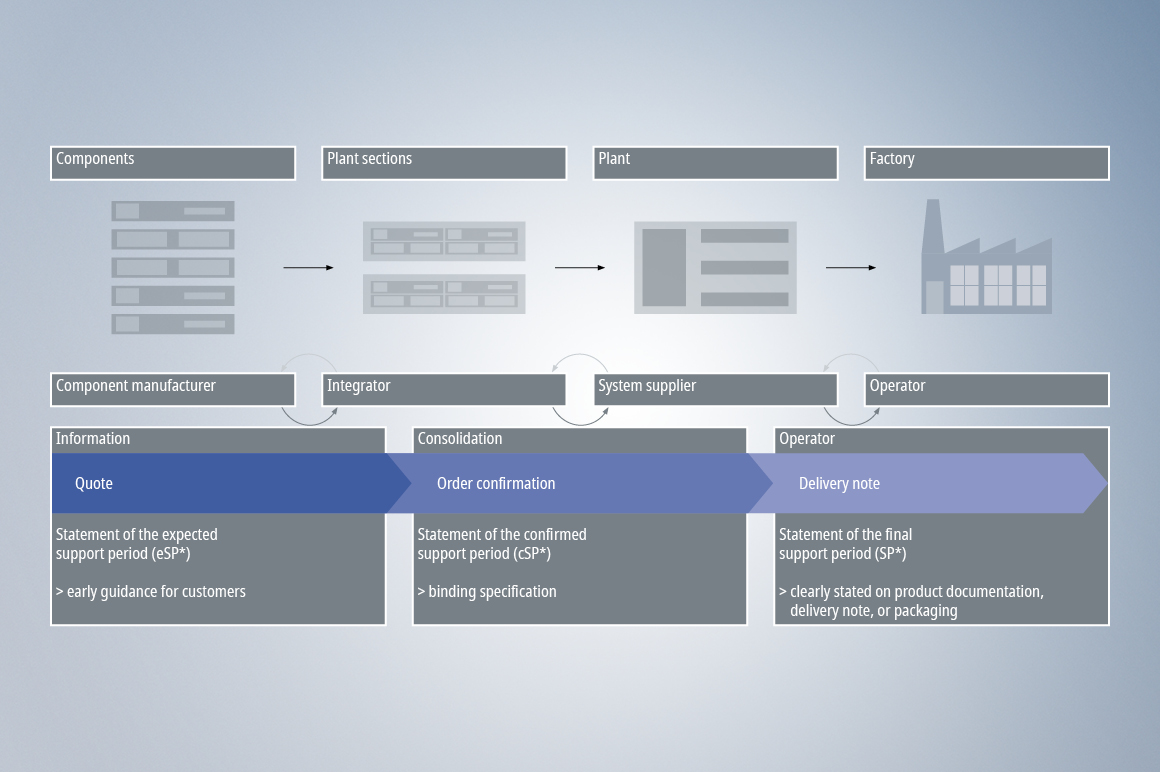
According to the CRA, the support period within the industrial supply chain must in future be notified in the quotation, communicated in the order confirmation and repeated on the delivery note. This will entail organizational effort, which may also have an impact on inventory management. Machine builders should prepare themselves accordingly.
A particular level of organizational effort may be required if a machine or system can only be offered or confirmed with a specific support period once reliable information is provided from the supply chain: for example, in the form of quotations with confirmed support periods for supplied components with a core function.
Machine builders must actively monitor and address vulnerabilities during the support period. This requires more than just monitoring relevant databases for cybersecurity vulnerabilities. Two more things are required:
- Acceptance and handling of reports of cybersecurity vulnerabilities by operators and researchers in the field, with only reports that have practical relevance to operations requiring any further action.
- Monitoring of existing cybersecurity vulnerabilities in the product and evaluating them in their overall context. For example, a component with a cybersecurity vulnerability may be installed, but this has no relevance to the cybersecurity of the machine or system.
Monitoring and addressing vulnerabilities cannot be delegated
Monitoring and addressing vulnerabilities is an indispensable organizational process that machine builders cannot delegate to their component suppliers. The reasons for this are obvious. Machines usually include components from different suppliers. There would therefore be an issue of which supplier should assess the process as a whole and perform the evaluation. In addition, component suppliers often do not know how their products will actually be used and whether this will produce any cybersecurity vulnerabilities for the respective machine or system. Component suppliers are therefore unable to guarantee the success of measures designed to fix vulnerabilities. As a rule, they do not have contractual relationships with the machine operators, are not involved in maintenance and have no knowledge of how the products are actually operated later on.
The new cybersecurity regulations will therefore create significant new overhead in the supply chain and this will cost money, even though this effort is sensible.
Effective cybersecurity is also a question of design
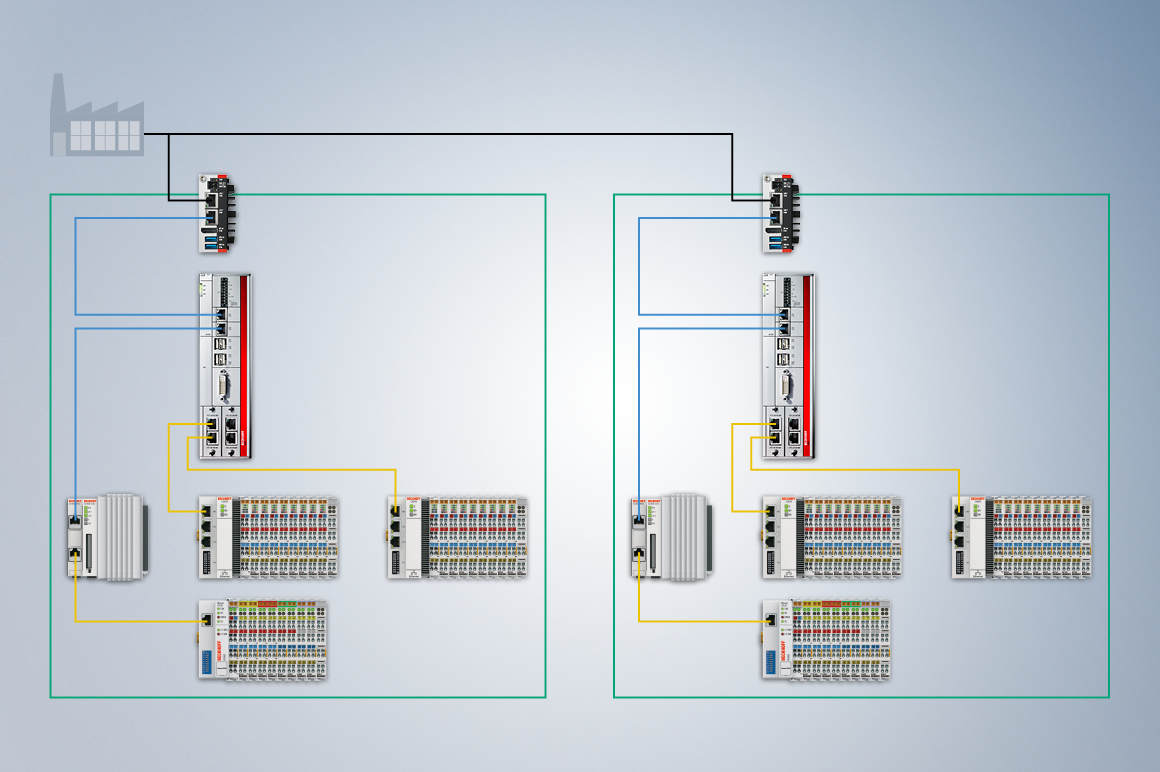
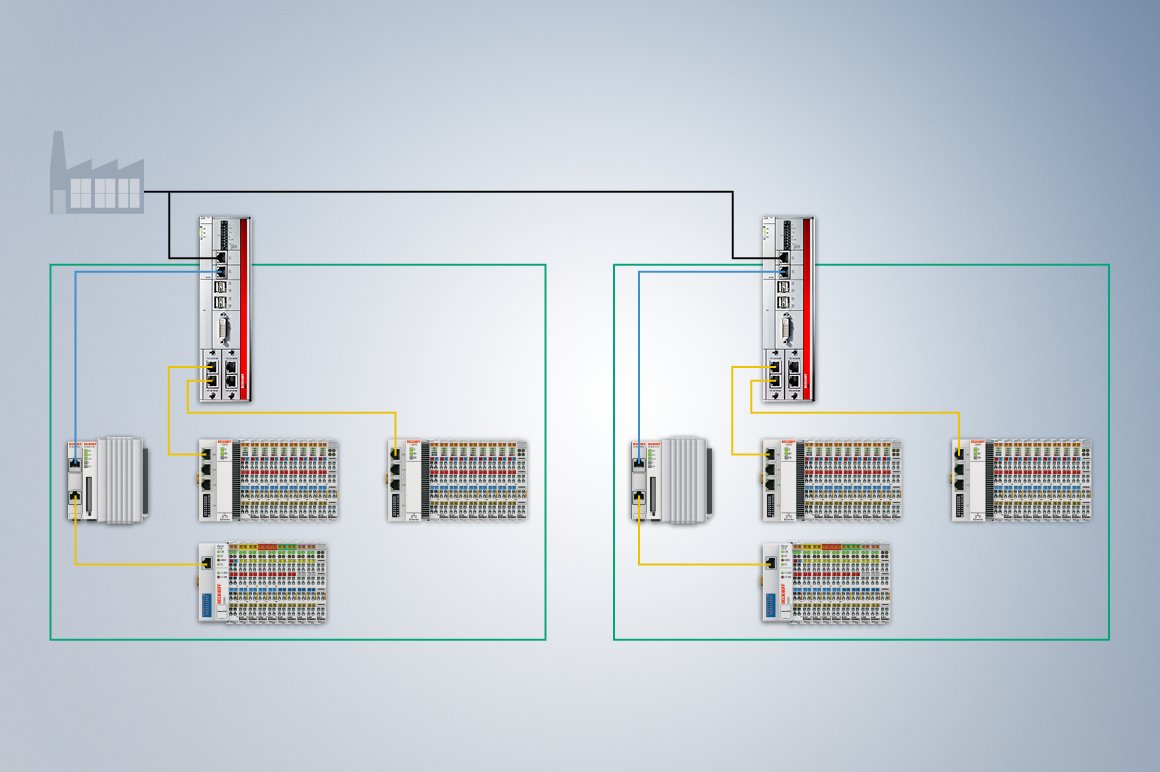
The aim is to embrace effective cybersecurity throughout the entire supply chain while generating as few additional costs as possible. This can be achieved, for example, by making improvements to the system design so that as few components as possible are required.
A simple measure can be to route all interactions with the system through one or more gateways and to route system cross-relationships via dedicated, protected lines. This allows the “inside” and “outside” to be separated. For products with professional operators in particular, it makes sense to reduce the potential vulnerabilities of the system by actively involving the system operators. For example, the risk of system manipulation by company employees can be eliminated by implementing organizational measures through the operator. In other words, the operator ensures that their staff cannot exceed certain limits.
The attack surface is thus reduced to the gateways and dedicated cross-connections that are well protected. It is then only these gateways and cross-connections that require risk assessments and organizational measures to be established to monitor and fix any vulnerabilities. The number of components to be monitored is reduced, and so is the number and impact of updates to be provided for the field.
Headquarters Germany
Beckhoff Automation GmbH & Co. KG
33415 Verl, Germany